ESET researchers discovered two new wiper malware families targeting Ukrainian organizations. The first cyberattack started a few hours prior to the Russian military invasion as ESET Research reported on its Twitter account, and after the DDoS attacks against major Ukrainian websites earlier that day.
These destructive attacks leveraged at least three components: HermeticWiper for wiping the data, HermeticWizard for spreading on the local network, and HermeticRansom acting as a decoy ransomware. Malware artifacts suggest that the attacks had been planned for several months. As the Russian invasion started, a second destructive attack against a Ukrainian governmental network started, using a wiper that ESET Research has named IsaacWiper.
“With regard to IsaacWiper, we are currently assessing its links, if any, with HermeticWiper. It is important to note that it was seen in a Ukrainian governmental organization that was not affected by HermeticWiper,” says ESET Head of Threat Research Jean-Ian Boutin.
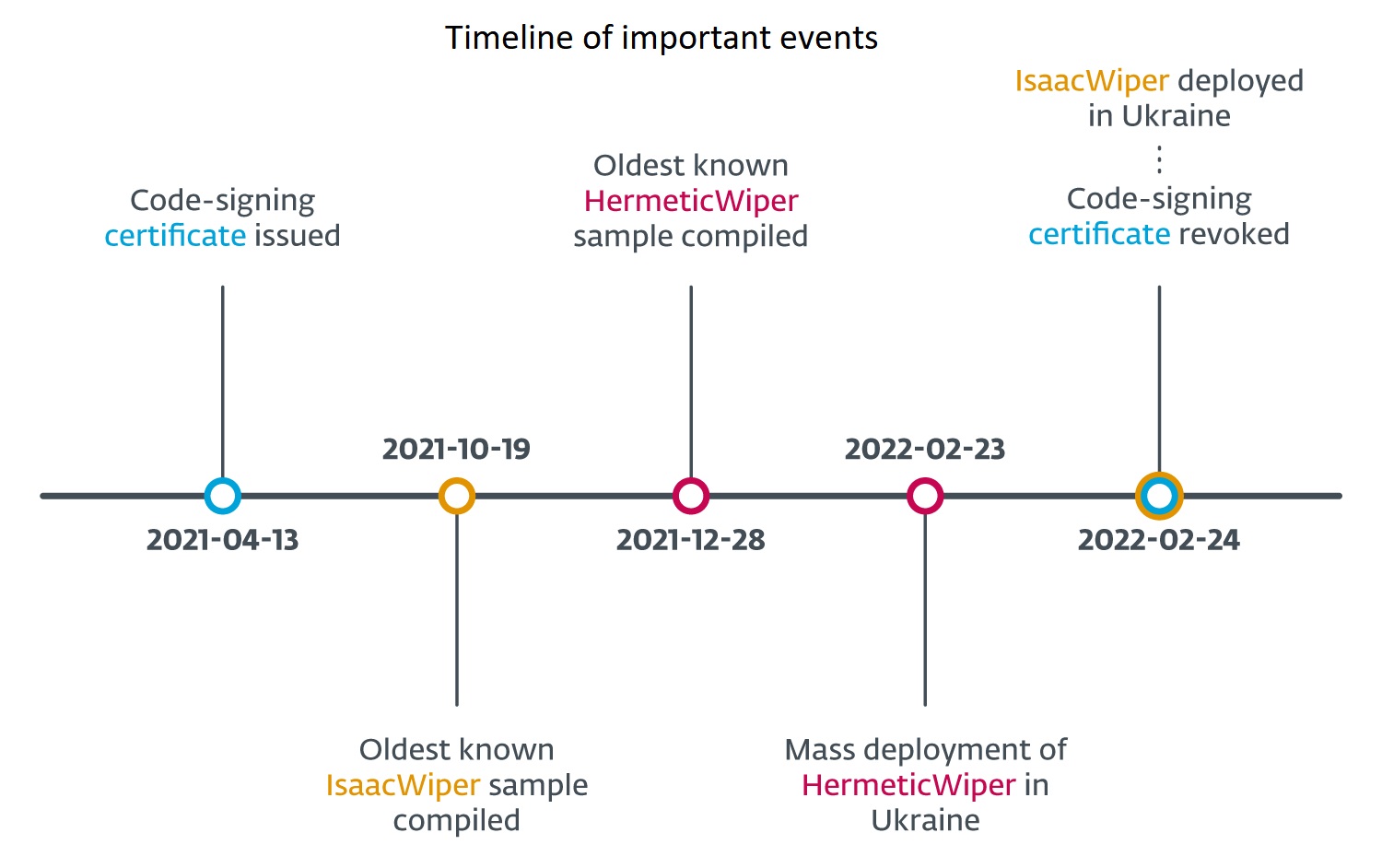
ESET researchers assess with high confidence that the affected organizations were compromised well in advance of the wiper’s deployment. “This is based on several facts: the HermeticWiper PE compilation timestamps, the oldest being December 28, 2021; the code-signing certificate issue date of April 13, 2021; and the deployment of HermeticWiper through the default domain policy in at least one instance, suggesting the attackers had prior access to one of that victim’s Active Directory servers,” says Boutin.
IsaacWiper appeared in ESET telemetry on February 24. The oldest PE compilation timestamp found was October 19, 2021, meaning that if its PE compilation timestamp was not tampered with, IsaacWiper might have been used in previous operations months earlier.
 In the case of HermeticWiper, ESET has observed artifacts of lateral movement inside the targeted organizations and that the attackers likely took control of an Active Directory server. A custom worm that ESET researchers named HermeticWizard was used to spread the wiper across the compromised networks. For the second wiper – IsaacWiper – the attackers used RemCom, a remote access tool, and possibly Impacket for movement inside the network.
In the case of HermeticWiper, ESET has observed artifacts of lateral movement inside the targeted organizations and that the attackers likely took control of an Active Directory server. A custom worm that ESET researchers named HermeticWizard was used to spread the wiper across the compromised networks. For the second wiper – IsaacWiper – the attackers used RemCom, a remote access tool, and possibly Impacket for movement inside the network.
Furthermore, HermeticWiper wipes itself from disk by overwriting its own file with random bytes. This anti-forensic measure is likely intended to prevent the analysis of the wiper in a post-incident analysis. The decoy ransomware HermeticRansom was deployed at the same time as HermeticWiper, potentially in order to hide the wiper’s actions.
Just a day after the deployment of IsaacWiper, attackers dropped a new version with debug logs. This may indicate that the attackers were unable to wipe some of the targeted machines and added log messages to understand what was happening.
ESET Research has not yet been able to attribute these attacks to a known threat actor due to the lack of any significant code similarity with other samples in the ESET malware collection.
The term “Hermetic” is derived from Hermetica Digital Ltd, a Cypriot company to which the code-signing certificate was issued. According to a report by Reuters, it seems that this certificate was not stolen from Hermetica Digital. Instead, it is likely that the attackers impersonated the Cypriot company in order to get this certificate from DigiCert. ESET Research requested the issuing company DigiCert to revoke the certificate immediately.












