Channel Post speaks to Alex Hinchliffe, the Threat Intelligence Analyst at Unit 42, Palo Alto Networks, about the recent Petya cyberattack
Why is the Petya attack more serious than the previous WannaCry attack?
There are a few of reasons why Petya is notable compared to WanaCrypt0r. First, it contained additional methods for spreading to other systems. Secondly, Petya, as with most malware, has no kill switch, which means that there was no method, like the one observed with WanaCrypt0r, to remotely and globally shut it down. Although there are claims that creating certain “dummy” files on systems would prevent Petya from creating them, and thus halt at least some of its activities, this is nowhere near as simple a solution as that seen with Wanacrypt0r’s kill switch.
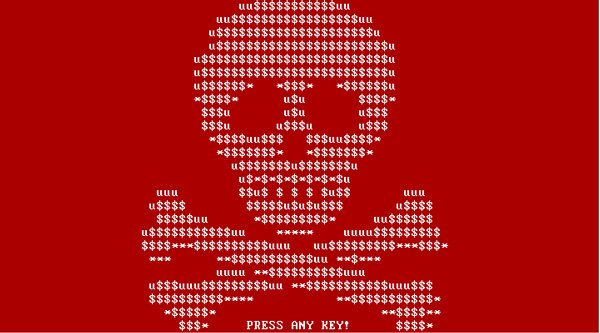
Finally, Petya attempt to modify the hard drive directly, by replacing the boot sector of the system until ransom is paid. This variant was no different, but compared to WanaCrypt0r, which simply encrypted files, performing such activities is inherently more dangerous and thus could be deemed more serious.
What is the cause of Petya’s spread across Europe?
The initial infection vector does seem to be via an update to an existing software programme, used extensively in Ukraine, which contained the malicious component. Although the Ukraine was heavily targeted, the infection then spread to other locations around Europe due to some companies having remote offices and facilities elsewhere that were connected to the corporate networks in the Ukraine.
What is the extent of the damage caused by the Petya ransomware cyberattack?
Various companies have been publicly named as affected by this attack and there are likely more. It’s believed that the impact is higher than WanaCrypt0r’s, especially in the Ukraine. Some of the companies reported are considered parts of critical national infrastructure, so the impacts could be quite far-reaching, however at present there appear to be no reports of knock-on effects on people, unlike with WanaCrypt0r, where some organizations operations were impacted.
Given the email address to communicate with has been taken down it would appear the attackers are going to leave many, if not all the, victims with encrypted systems.