By Rick Holland, VP Strategy at Digital Shadows
Late on 27 June, the New York Times reported that a number of Ukrainian banks and Ukrenergo, the Ukrainian state power distributor, had been affected by unidentified malware which caused significant operational disruption. Multiple security vendors and independent researchers subsequently identified the malware as a wormable ransomware variant with functional and technical similarities to Petya.

Based on these similarities and continuing confusion, the malware has been dubbed Nyetya, Petna, ExPetr, and NotPetya, among others. It has been linked with a large number of infections, a significant proportion of which (around 60% according to statistics published by Kaspersky) affected machines in Ukraine, though at the time of writing the overall number of infections is not known.
How NotPetya Works
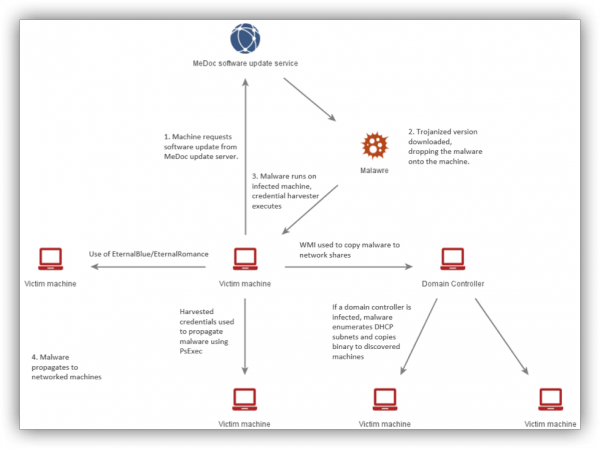
On 27 June, a social media account used by the National Police of Ukraine Cyberpolice Department, suggested that the reported infections originated from a compromised software update delivered to users through MeDoc, a Ukrainian accounting software provider. While MeDoc has denied this, Microsoft has confirmed that a small number of infections were the result of malware being delivered to machines by the MeDoc’s software update process. Once the malware was installed, intra-network propagation functions enabled it to rapidly spread between networked machines over the following vectors:
- EternalBlue and EternalRomance exploits: EternalBlue and EternalRomance are exploits for SMB remote code execution vulnerabilities (CVE-2017-0144 and CVE-2017-0145) leaked by the Shadow Brokers in April These exploits were reportedly used to propagate between networked machines running SMB. Patches for these vulnerabilities were released by Microsoft in March (MS17-010) and in May.
- PsExec: The ransomware used a tool similar to Mimikatz to harvest user credentials. These credentials were then passed to an older version of the PSExec Windows tool which was dropped by the malware. This tool then attempted to use PowerShell remote functionality to copy itself onto a target machine and begin execution.
- Windows Management Instrumentation (WMI): The malware also enumerated Windows network shares with WMI and attempted to launch a copy of itself on any discovered network shares.
Figure 1 below shows a possible deployment and propagation process for the malware.
Once installed, the malware functioned similarly to Petya, checking for the availability of Administrator privileges by using the Windows API AdjustTokenPrivileges function. If this was successful, the malware would overwrite the infected machine’s Master Boot record (MBR), rendering it unbootable.
If this was not possible, AES-128 keys were used to encrypt each individual file, with the AES keys subsequently being encrypted using an RSA-2048 public key. To obtain the private RSA key necessary to recover the AES keys, victims were instructed to transfer $300 USD in Bitcoin to a specified Bitcoin ID and send their wallet ID and victim ID number in an email to a specified address.
Why?
While the malware’s functionality has reportedly made it highly effective at propagating to machines within a local network, it has been reported as having no function for spreading outside of these local networks. It was therefore assessed as likely to be much more effective for conducting targeted attacks than wCry (AKA WannaCry).
In the case of NotPetya, it is highly likely that the ransom payment method was never intended to result in revenue for attackers or the recovery of victim data. Although the email service provider with which the account was registered has publicly announced that this account has been disabled, it has subsequently been reported that victim ID numbers were pseudo randomly generated rather than being derived from the RSA key used for AES key encryption.
This indicates that it would not be possible for the threat actors to provide victims with the correct decryption key, even if a victim had paid the ransom and succeeded in making contact. Furthermore, Matt Suiche has reported that, unlike Petya, which encrypts an infected machine’s MBR in a reversible manner, this malware reportedly irreversibly overwrote 24 sector blocks of the MBR section of an infected machine’s disk, rendering it permanently inoperable.
With monetary gain as a motivation out the picture, the most likely motivation left for NotPeyta’s behavior is destructive malicious intent. Malicious intent is not synonymous with any single ‘class’ of threat actor, hacktivists ‘do it for the lulz”; nation state actors conduct malicious cyber-attacks to fulfill geostrategic objectives. With this in mind, NotPeyta does demonstrate an advanced understanding of how to mount a wide spread hard hitting cyber-attack, and to capitalize on this attack with maximum media exposure.
Who
Clues lie in the geopolitical context and the initial target geography of the malware. Kaspersky Labs have claimed a 60/30% split (total number of infections unknown) between Ukraine and Russia. Additionally, the initial attack occurred during the Ukrainian holiday celebrating independence from Russia. If one subscribes to the theory that Russian state or affiliated actors are responsible, this had the tactical effect of delaying a coherent response from Ukrainian defenders and strategically punishing Ukraine for its independence from Russia. Although these facts are interesting – and they do suggest that the malware was actively aimed at the Ukrainian economy – they are circumstantial and do not conclusively link the incident to any particular nation state. Attribution is and will continue to be a challenge.
The technology behind this attack is well within the range of many hacktivists and cyber criminals, and so these details have less diagnostic value when considering the ‘who’. Although speculative, there are other factors to consider: the supply chain compromise, efforts at obfuscation (hiding the wiper as ransomware), the geography that the malware was deployed in, and the timing of the deployment with Ukrainian national holidays. These point towards an attacker with political motivations behind the attack. It seems that the actor behind the NotPetya variant was politically motivated with an exceptional appetite to conduct cyber-attacks against specific organizations within the Ukraine target geography.
Longer-Term Implications
So where does this incident leave the longer-term assessment of the implications of NotPetya?
- Prepare for stray bullets. Many organizations were impacted by the NotPeyta campaign. The interconnectivity of modern systems and the ubiquity of applications means that enterprises could find themselves the victims of attacks not specifically targeting their organizations.
- The bar for cyber-attacks keeps getting lower. The availability of leaked tools from the NSA and HackingTeam, coupled with ‘how to’ manuals, means that threat actors will have access to powerful tools that they can iterate from and leverage to aggressively accomplish their goals.
Sadly, cyber-attacks of this nature are not uncommon and so businesses, governments and of course consumers need to take steps to protect themselves against ransomware attacks.
- The “basics” aren’t easy, but they should not be forgotten. Both NotPetya and the earlier WannaCry exploited basic and known security vulnerabilities, so segmenting networks and applying basic patching cycles will go a long way to mitigating threats such as this. This will go a long way in mitigating the ‘stray bullet’ factor outlined above.
- Think about the soft factors. Defense is not just about technical indicators and warning anymore, ‘soft’ factors such as motivation and geostrategic issues are now not just ‘nice to haves’ but are increasingly critical in the response to malware like NotPetya.
- Plan to fail. No amount of good security will entirely remove the risk posed by cyberattacks so it is critical to backup critical data and systems on a regular basis and ensure crisis management and comprehensive data recovery plans are in place and practiced. Extortion and destructive malware response should be in your incident response playbooks.
- If you aren’t already doing so, think about the digital risks associated with your supply chain. Sure, not all suppliers are attack vectors for targeted attacks, but many suppliers do not have the mature levels of security. Regardless of the alleged culpability of MEDoc, the deployment mechanism does highlight the attention that we all need to start paying to supply chain compromise.
- Defense in depth. Digital Shadows advocate using a ‘defense in depth’ strategy guided by four main principles: configuring host-based firewalls and using IP-whitelisting measures, segmenting networks and restricting workstation-to-workstation communication, applying patches and disabling unneeded legacy features, and restricting access to important data to only those who are required to have it.
WannaCry and NotPeyta are a sign of things to come, and you can expect attackers will improve their future campaigns.












