The WannaCry ransomware is not dead yet and another large scale ransomware attack is making chaos worldwide. The attack is shutting down computers at corporate houses, power supplies, and banks across Russia, Ukraine, Spain, France, UK, India, and Europe and demanding $300 in bitcoins.
According to multiple sources, a new variant of Petya ransomware, also known as Petwrap, is spreading rapidly with the help of same Windows SMBv1 vulnerability that the WannaCry ransomware abused to infect 300,000 systems and servers worldwide in just 72 hours last month. Petya is a ransomware and works very differently from any other ransomware malware. Unlike other traditional ransomware, Petya does not encrypt files on a targeted system one by one.
Instead, Petya reboots victims computers and encrypts the hard drive’s master file table (MFT) and renders the master boot record (MBR) inoperable, restricting access to the full system by seizing information about file names, sizes, and location on the physical disk. Petya ransomware replaces the computer’s MBR with its own malicious code that displays the ransom note and leaves computers unable to boot.
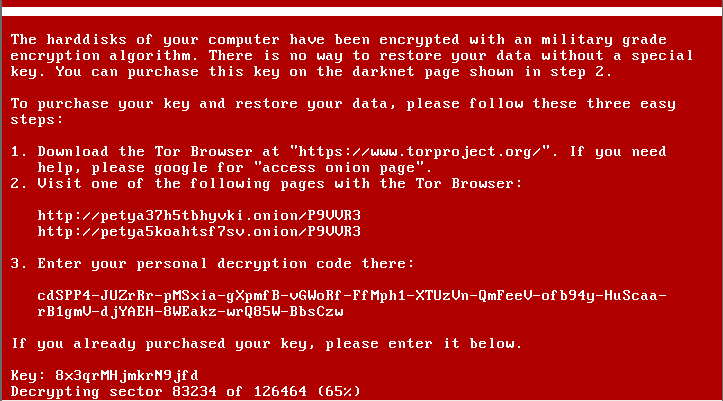
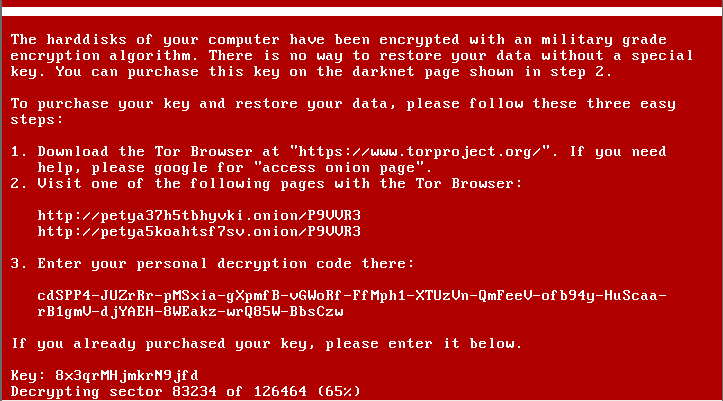
Screenshots of the latest Petya infection, shared on Twitter, shows that the ransomware displays a text, demanding $300 worth of Bitcoins. Here’s what the text read:
“If you see this text, then your files are no longer accessible, because they are encrypted. Perhaps you are busy looking for a way to recover your files, but don’t waste your time. Nobody can recover your files without our decryption service.”
According to a recent VirusTotal scan, currently, only 16 out of 61 anti-virus services are successfully detecting the Petya ransomware malware. Petya ransomware has already infected — Russian state-owned oil giant Rosneft, Ukrainian state electricity suppliers, “Kyivenergo” and “Ukrenergo,” in past few hours.
“We were attacked. Two hours ago, we had to turn off all our computers. We are waiting for permission from Ukraine’s Security Service (SBU) to switch them back on,” Kyivenergo’s press service said. There are reports from several banks, including National Bank of Ukraine (NBU) and Oschadbank, as well as other companies confirming they have been hit by the Petya ransomware attacks.
Maersk, an international logistics company, has also confirmed on Twitter that the latest Petya ransomware attacks have shut down its IT systems at multiple locations and business units. “We can confirm that Maersk IT systems are down across multiple sites and business units. We are currently asserting the situation. The safety of our employees, our operations and customers’ business is our top priority. We will update when we have more information,” the company said.
The ransomware also impacts multiple workstations at Ukrainian branch’s mining company Evraz. The most severe damages reported by Ukrainian businesses also include compromised systems at Ukraine’s local metro and Kiev’s Boryspil Airport.
Three Ukrainian telecommunication operators, Kyivstar, LifeCell, Ukrtelecom, are also affected in the latest Petya attack. At the time of writing, 17 victims have paid in Bitcoin to ‘1Mz7153HMuxXTuR2R1t78mGSdzaAtNbBWX‘ address for decrypting their files infected by Petya, which total roughly $4025.
Symantec, the cyber security company, has also confirmed that Petya ransomware is exploiting SMBv1 EternalBlue exploit, just like WannaCry, and taking advantage of unpatched Windows machines. “Petya ransomware successful in spreading because it combines both a client-side attack (CVE-2017-0199) and a network based threat (MS17-010),” security researcher using Twitter handle HackerFantastic tweeted.
EternalBlue is a Windows SMB exploit leaked by the infamous hacking group Shadow Brokers in its April data dump, who claimed to have stolen it from the US intelligence agency NSA, along with other Windows exploits. Microsoft has since patched the vulnerability for all versions of Windows operating systems, but many users remain vulnerable, and a string of malware variants are exploiting the flaw to deliver ransomware and mine cryptocurrency.
Just three days ago, news agencies reported that the latest WannaCry attack had hit Honda Motor Company and around 55 speed and traffic light cameras in Japan and Australia, respectively.